pentestbox 下安装whatweb后,报IPADDR模块没有配置,无法运行(whatweb安装过程略)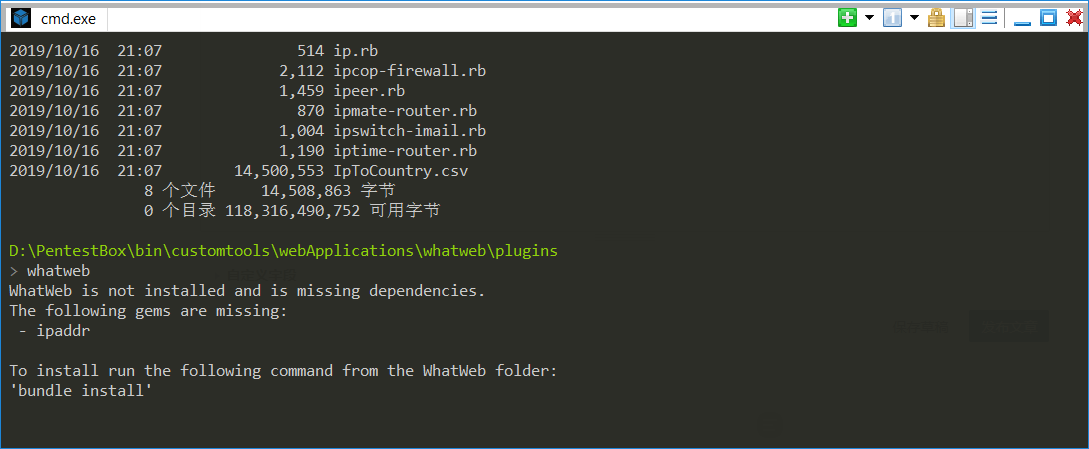
查阅网络无果,根据提示,进到whatweb安装目录如D:\PentestBox\bin\customtools\webApplications\whatweb\:,执行
D:\PentestBox\bin\customtools\webApplications\whatweb\plugins
> bundle install
Fetching source index from https://rubygems.org/
Retrying fetcher due to error (2/4): Bundler::Fetcher::CertificateFailureError Could not verify the SSL certificate for https://rubygems.org/.
There is a chance you are experiencing a man-in-the-middle attack, but most likely your system doesn't have the CA certificates needed for verification. For information about OpenSSL certificates, see http://bit.ly/ruby-ssl. To connect without using SSL, edit your Gemfile sources and change 'https' to 'http'.
Retrying fetcher due to error (3/4): Bundler::Fetcher::CertificateFailureError Could not verify the SSL certificate for https://rubygems.org/.
There is a chance you are experiencing a man-in-the-middle attack, but most likely your system doesn't have the CA certificates needed for verification. For information about OpenSSL certificates, see http://bit.ly/ruby-ssl. To connect without using SSL, edit your Gemfile sources and change 'https' to 'http'.
Retrying fetcher due to error (4/4): Bundler::Fetcher::CertificateFailureError Could not verify the SSL certificate for https://rubygems.org/.
There is a chance you are experiencing a man-in-the-middle attack, but most likely your system doesn't have the CA certificates needed for verification. For information about OpenSSL certificates, see http://bit.ly/ruby-ssl. To connect without using SSL, edit your Gemfile sources and change 'https' to 'http'.
Could not verify the SSL certificate for https://rubygems.org/.
There is a chance you are experiencing a man-in-the-middle attack, but most
likely your system doesn't have the CA certificates needed for verification. For
information about OpenSSL certificates, see http://bit.ly/ruby-ssl. To connect
without using SSL, edit your Gemfile sources and change 'https' to 'http'.
发现执行代码报错,根据提示找到whatweb安装目录下的Gemfile文件,用记事本打开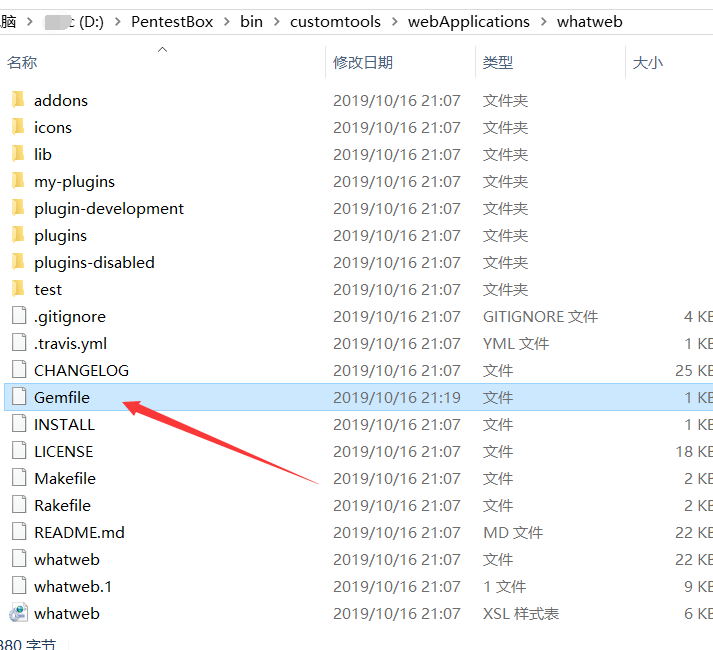
找到其中的
##
source 'https://rubygems.org' #将https改为http
重新运行bundle install执行安装。问题解决
D:\PentestBox\bin\customtools\webApplications\whatweb
> bundle install
Fetching gem metadata from http://rubygems.org/..........
Fetching version metadata from http://rubygems.org/..
Resolving dependencies...
Installing rake 13.0.0
Gem::InstallError: rake requires Ruby version >= 2.2.
Installing public_suffix 4.0.1
Gem::InstallError: public_suffix requires Ruby version >= 2.3.
Installing ast 2.4.0
Using bundler 1.11.2
Installing thor 0.20.3
Installing coderay 1.1.2
Installing ipaddr 1.2.2
Installing jaro_winkler 1.5.3 with native extensions
Installing json 2.2.0 with native extensions
Installing method_source 0.9.2
Installing minitest 5.12.2
Gem::InstallError: minitest requires Ruby version ~> 2.2.
Installing parallel 1.18.0
Gem::InstallError: parallel requires Ruby version >= 2.2.
Installing rainbow 3.0.0
Installing rb-readline 0.5.5
Installing rdoc 6.2.0
Gem::InstallError: rdoc requires Ruby version >= 2.2.2.
Installing ruby-progressbar 1.10.1
Installing unicode-display_width 1.6.0
An error occurred while installing rake (13.0.0), and Bundler cannot continue.
Make sure that `gem install rake -v '13.0.0'` succeeds before bundling.
D:\PentestBox\bin\customtools\webApplications\whatweb
> whatweb
.$$$ $. .$$$ $.
$$$$ $$. .$$$ $$$ .$$$$$$. .$$$$$$$$$$. $$$$ $$. .$$$$$$$. .$$$$$$.
$ $$ $$$ $ $$ $$$ $ $$$$$$. $$$$$ $$$$$$ $ $$ $$$ $ $$ $$ $ $$$$$$.
$ `$ $$$ $ `$ $$$ $ `$ $$$ $$' $ `$ `$$ $ `$ $$$ $ `$ $ `$ $$$'
$. $ $$$ $. $$$$$$ $. $$$$$$ `$ $. $ :' $. $ $$$ $. $$$$ $. $$$$$.
$::$ . $$$ $::$ $$$ $::$ $$$ $::$ $::$ . $$$ $::$ $::$ $$$$
$;;$ $$$ $$$ $;;$ $$$ $;;$ $$$ $;;$ $;;$ $$$ $$$ $;;$ $;;$ $$$$
$$$$$$ $$$$$ $$$$ $$$ $$$$ $$$ $$$$ $$$$$$ $$$$$ $$$$$$$$$ $$$$$$$$$'
WhatWeb - Next generation web scanner version 0.5.0.
Developed by Andrew Horton (urbanadventurer) and Brendan Coles (bcoles)
Homepage: https://www.morningstarsecurity.com/research/whatweb
Usage: whatweb [options] <URLs>
<TARGETs> Enter URLs, hostnames, IP addresses, filenames or
IP ranges in CIDR, x.x.x-x, or x.x.x.x-x.x.x.x
format.
--input-file=FILE, -i Read targets from a file.
--aggression, -a=LEVEL Set the aggression level. Default: 1.
1. Stealthy Makes one HTTP request per target and also
follows redirects.
3. Aggressive If a level 1 plugin is matched, additional
requests will be made.
--list-plugins, -l List all plugins.
--info-plugins, -I=[SEARCH] List all plugins with detailed information.
Optionally search with a keyword.
--verbose, -v Verbose output includes plugin descriptions.
Note: This is the short usage help. For the complete usage help use -h or --help.



评论 (0)